- CISA rates the Zero vulnerability as medium severity (CVSS 6.4) and the Yadea vulnerability as high (CVSS 7.3)
- Zero Motorcycles plans a firmware update for May 2026; Yadea has not yet released a patch
- Both vulnerabilities require physical proximity to the vehicle
Connected vehicles offer convenience but also bring new risks. Navigation, vehicle diagnostics via app, over-the-air updates, and telemetry data are now standard features on modern electric motorcycles. Two recent cases made public by the U.S. Cybersecurity and Infrastructure Security Agency (CISA) in April 2026 demonstrate that this connectivity can also be exploited. Affected are the American electric motorcycle manufacturer Zero Motorcycles and the Chinese two-wheeler group Yadea, one of the world’s largest manufacturers of electric scooters and e-bikes.

What Vulnerability Was Discovered at Zero Motorcycles?
The security flaw CVE-2026-1354 affects all Zero Motorcycles firmware versions up to and including version 44. It was discovered by security researchers Persephone Karnstein and Mitchell Marasch from Bureau Veritas Cybersecurity North America, who reported their findings to CISA and presented them at the BSides Seattle 2026 security conference.
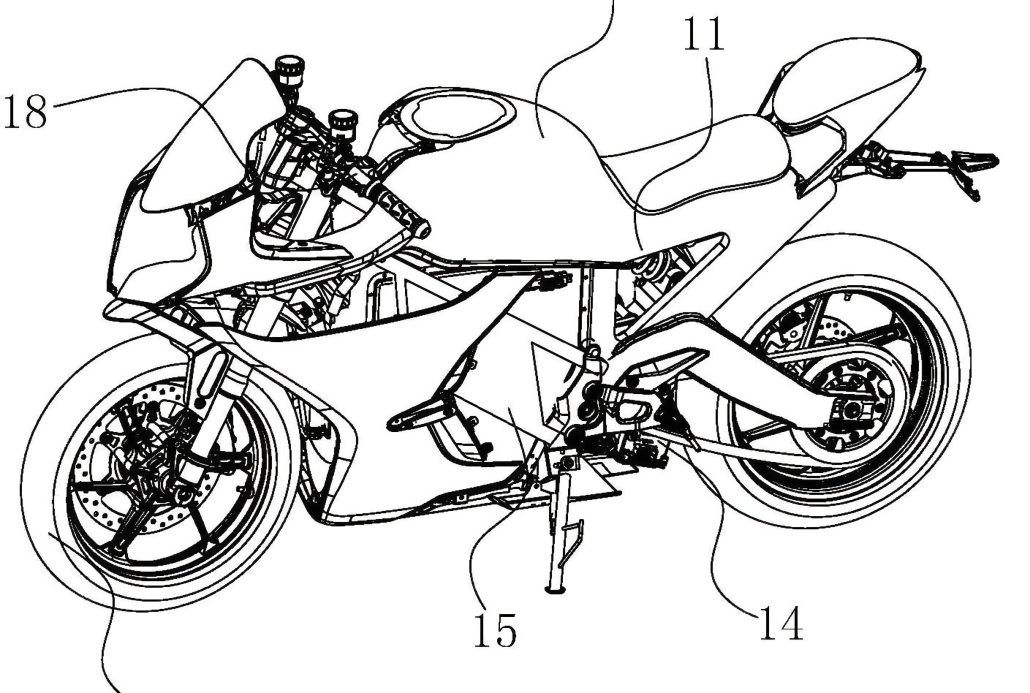
The problem lies in the Bluetooth pairing function of the motorcycles. According to Dinesh Shetty, Director of Security Engineering at Bureau Veritas, the pairing mode can be activated by pressing the mode button for about five seconds, or when the motorcycle has never been paired before. During this time window, the key exchange does not verify who is connecting. An attacker within Bluetooth range could pair their own device, and the motorcycle would accept the connection as legitimate.
CISA classifies the vulnerability as medium severity with a CVSS 3.1 score of 6.4. The technical classification CWE-322 describes a key exchange without authentication of the participating devices. For successful exploitation, several conditions must be met simultaneously: the motorcycle must be in pairing mode, the attacker must be in close proximity, must fully understand the pairing process, and must remain within range throughout the entire duration of a firmware upload. CISA therefore rates the attack complexity as high.
What Could an Attacker Do with Manipulated Firmware?
After a successful pairing, an attacker could upload manipulated firmware to the motorcycle via the over-the-air update function. According to Dinesh Shetty from Bureau Veritas, the motorcycle’s main microcontroller controls safety-critical functions. These include torque control, regenerative braking, the contactors for motor power supply, and battery management. Anyone who can load their own firmware onto this controller can manipulate all of these systems.
Shetty describes the potential impact in plain terms: on a vehicle at highway speed, the throttle response could be altered, braking behavior impaired, or the battery’s thermal protection functions manipulated. Additionally, the control board has access to a cellular modem for GPS and telemetry that could theoretically be repurposed for remote control. Shetty emphasizes that this is not about changing the color of the dashboard, but about firmware that controls the physical behavior of the vehicle.
According to CISA, no cases are known in which this vulnerability has actually been exploited.

What Does Zero Motorcycles Recommend to Its Customers?
Zero Motorcycles says it has investigated the vulnerability and recommends that customers only perform smartphone pairing in secure locations where no one else could attempt to pair simultaneously. The complete pairing process should be finished and the successful connection confirmed. Physical keys should be kept secure, and the motorcycle should not be left unattended with the ignition on.
Zero Motorcycles has announced a firmware update to address the vulnerability for May 2026.
How Does the Attack on the Yadea T5 Work?
Two days after the Zero advisory, CISA published a separate warning for the Yadea T5 electric scooter on April 23, 2026. The vulnerability CVE-2025-70994 was discovered by security researcher Ashen Chathuranga and reported to both MITRE and CISA.
The problem affects the keyless entry system of the Yadea T5. It uses the EV1527 protocol, a fixed-code radio standard without rolling codes or cryptographic challenge-response mechanisms. In simple terms, the key fob sends the same code with every button press. An attacker within radio range can intercept any legitimate transmission, such as a lock command, and mathematically derive a different command from the captured data, including unlock and start commands. According to discoverer Ashen Chathuranga, after intercepting a single command, the attacker can immediately synthesize a new one and perform a replay attack.
The CISA-ADP rates the vulnerability with a CVSS 3.1 score of 7.3, corresponding to a “high” severity level. Unlike the Zero vulnerability, the attack complexity is low, no special privileges are needed, and a public proof-of-concept already exists. The vulnerability is listed under CWE-1390 (Weak Authentication). According to CISA, all versions of the Yadea T5 from model year 2024 onward are affected.
The consequence is concrete: an attacker could unlock, start, and steal the scooter. The required hardware, a simple Software Defined Radio (SDR) receiver, is available for less than 50 US dollars (approximately 46 euros) according to expert reports. The attack works over radio frequencies in the 315 MHz or 433 MHz ISM band.

Has Yadea Responded?
Yadea has neither released a patch nor responded to press inquiries from SecurityWeek. CISA recommends that Yadea T5 owners keep their systems up to date and additionally protect their vehicle with external mechanical locks. Yadea can be reached through the company’s contact page.
Compared to Zero Motorcycles, where a firmware update has at least been announced, fixing the Yadea vulnerability requires a fundamental redesign of the keyless entry system, according to security experts, since the EV1527 protocol used is inherently incapable of providing secure authentication. Modern systems instead use rolling codes, where the radio code changes with each use.
Why Does This Issue Also Affect Riders Outside the U.S.?
Both vulnerabilities were reported to CISA in the United States, a U.S. agency. Zero Motorcycles is headquartered in the U.S., Yadea in China. However, both companies sell their vehicles worldwide. CISA assigns both cases to the “Transportation Systems” sector and notes the deployment area as “Worldwide.” Regardless of location, owners of affected vehicles should follow developments and install available updates promptly.
These two cases join a series of cybersecurity incidents in the motorcycle and vehicle industry. In the past, Harley-Davidson was affected by a data leak and Kawasaki Europe by a ransomware attack. As electric two-wheelers become increasingly connected, their attack surface grows as well — from Bluetooth interfaces to app connections to keyless entry systems.
Frequently Asked Questions
-
Which Zero Motorcycles models are affected by the security vulnerability?
According to CISA, the vulnerability CVE-2026-1354 affects all Zero Motorcycles firmware versions up to and including version 44. CISA classifies the area as critical infrastructure in the transportation systems sector. A firmware update has been announced for May 2026.
-
Can the Yadea T5 be hacked over the internet?
No, both vulnerabilities require physical proximity to the vehicle. The Zero vulnerability requires the attacker to be within Bluetooth range, while the Yadea T5 requires radio range of the key system in the 315 MHz or 433 MHz band. CISA explicitly confirms that the Yadea vulnerability cannot be exploited remotely.
-
What should Yadea T5 owners do now?
Since Yadea has not yet provided a patch, CISA recommends additionally securing the vehicle with mechanical locks and checking the manufacturer’s official channels for updates. The key fob should be stored in a signal-blocking pouch to make intercepting radio signals more difficult.
-
How dangerous is the Zero Motorcycles vulnerability in practice?
CISA rates the attack complexity as high. The attacker must be within Bluetooth range, know the pairing process precisely, and remain nearby throughout the entire firmware upload. According to Bureau Veritas, however, a motivated and well-equipped attacker could carry out the attack.

- Milestone Ride 6 (Day One Edition) – Sony PlayStation 5 – Rennspiel – PEGI 3